Connect with Customers.
Disconnect from Risks.
DNS Defense
DNS Defense is a SaaS service that works on the DNS systems you have already, or will in the future, including Active Directory, BIND, and more. With DNS Defense your PDNS will identify and stop threats early, before they cause damage. Powered by continuous updates from hundreds of Threat Intelligence sources, the platform knows and tracks the infrastructure used by cyber criminals to conduct attacks, and keeps your network devices updated to block or redirect those malicious and unwanted DNS requests.
Add in predictive feedback loops and customer-specific block and allow lists, and you have ThreatSTOP's highly adaptive DNS protection. There is no new equipment to buy, or threat intelligence sources to tap into - ThreatSTOP provides the data, the integrations, and the automation to keep your DNS systems tuned for the newest threats.
- Makes what you have better (works on everything you have now and in the future - Active Directory, BIND, Infoblox, etc.)
- Provides granular, proactive DNS threat protection
- Supports highly customizable DNS (RPZ) responses
- MyDNS agent extends protection to remote or roaming Win/Mac endpoints
- Includes powerful reporting and security research tools
We incorporate hundreds of threat intelligence feeds that are human & machine curated, delivering the broadest coverage in the industry of IP addresses and domains.
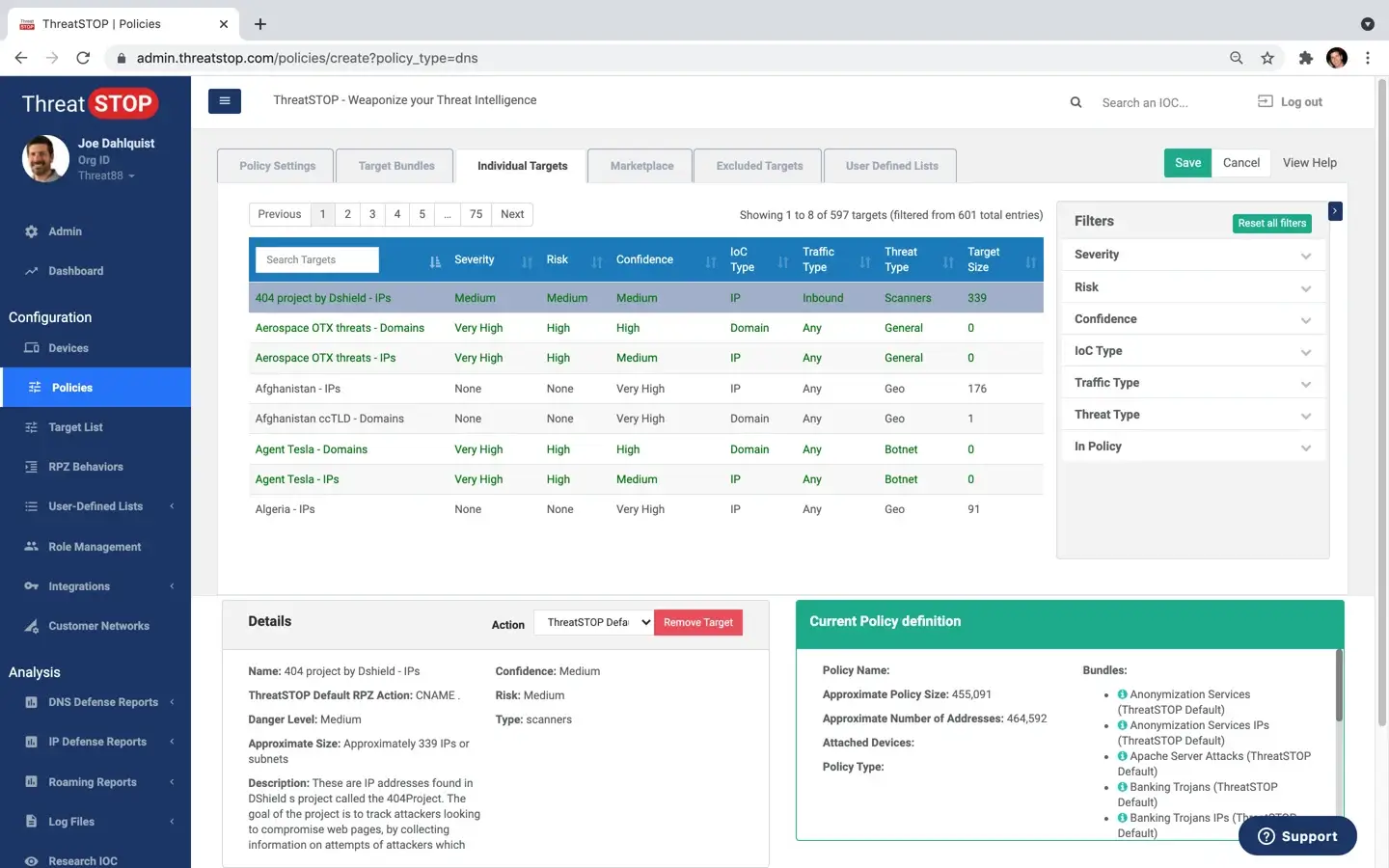
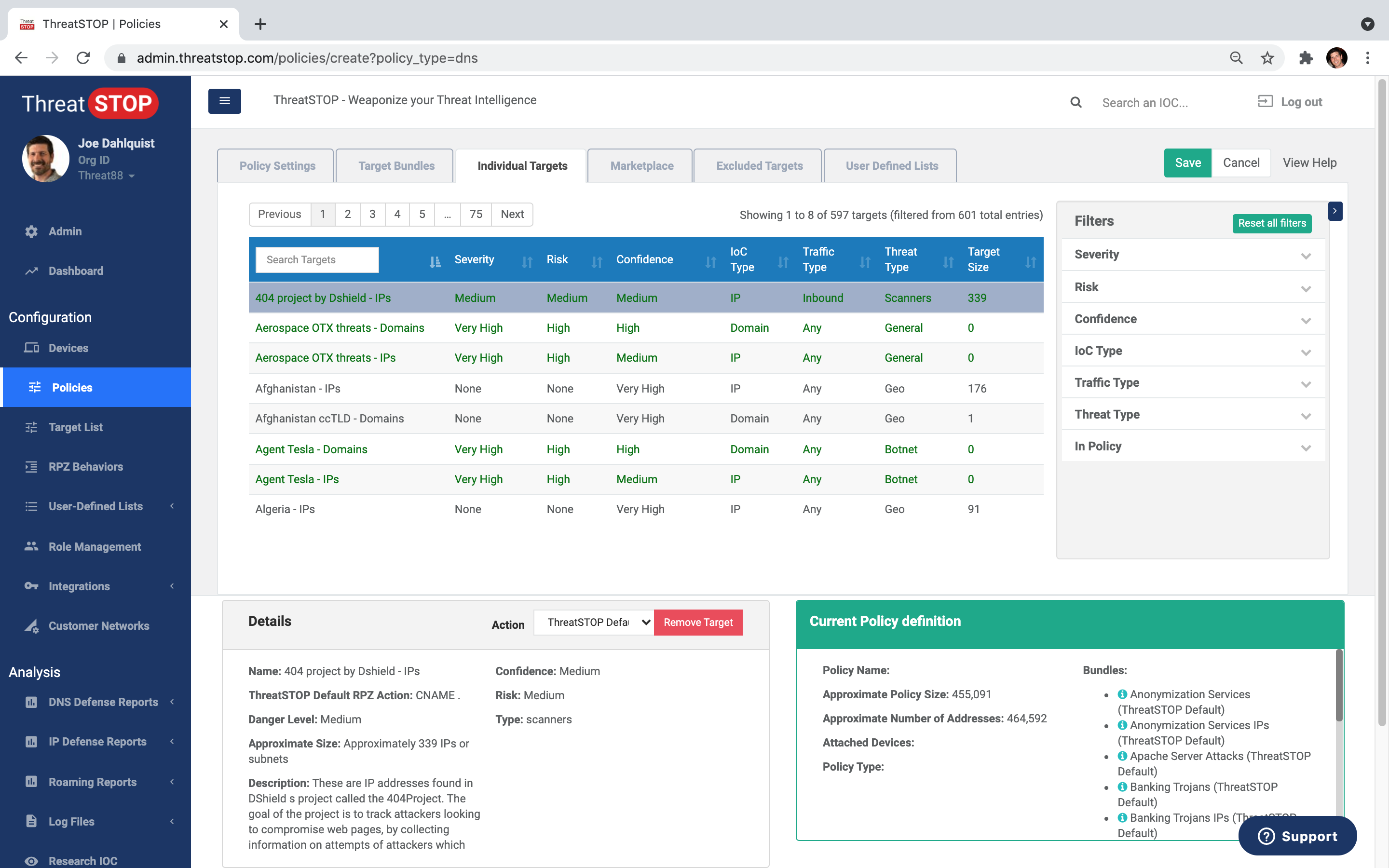
Get 600+ fully customizable policies in selectable categories. Tailor your own custom block & allowlists.
Automated policy updates NGFW, DNS, Router, Switch, IDP, WAF, SIEM and more.
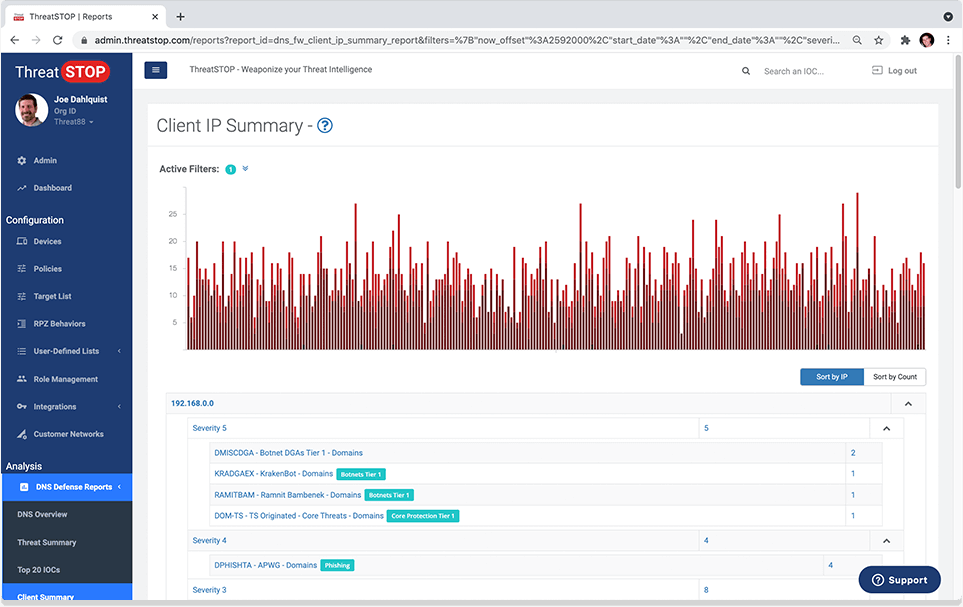
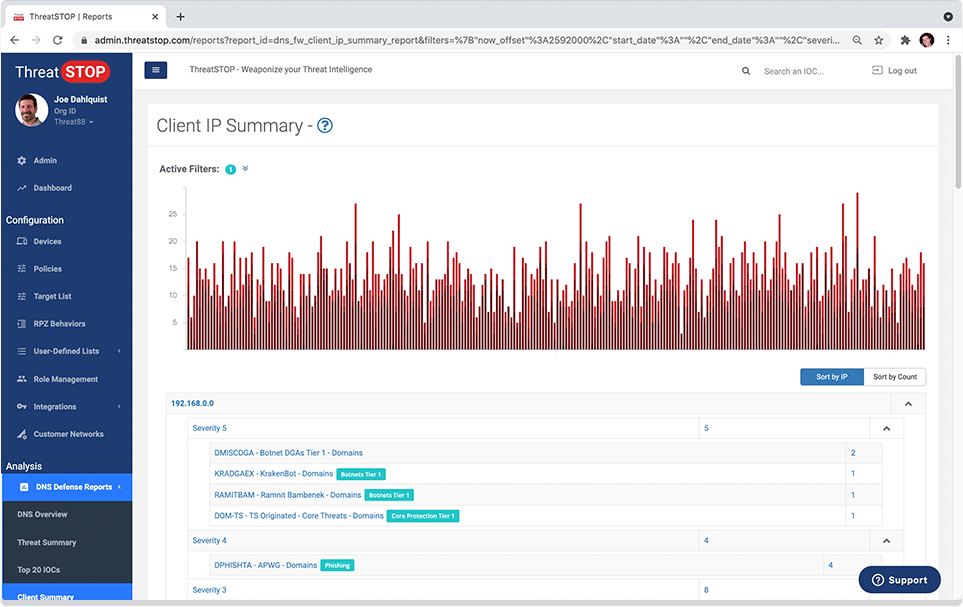
View & analyze blocked threats. Identify affected client devices. Custom email reports & alerts.
Intelligence collection
We incorporate hundreds of threat intelligence feeds that are human & machine curated, delivering the broadest coverage in the industry of IP addresses and domains.
Policy customization
Get 600+ fully customizable policies in selectable categories. Tailor your own custom block & allowlists.
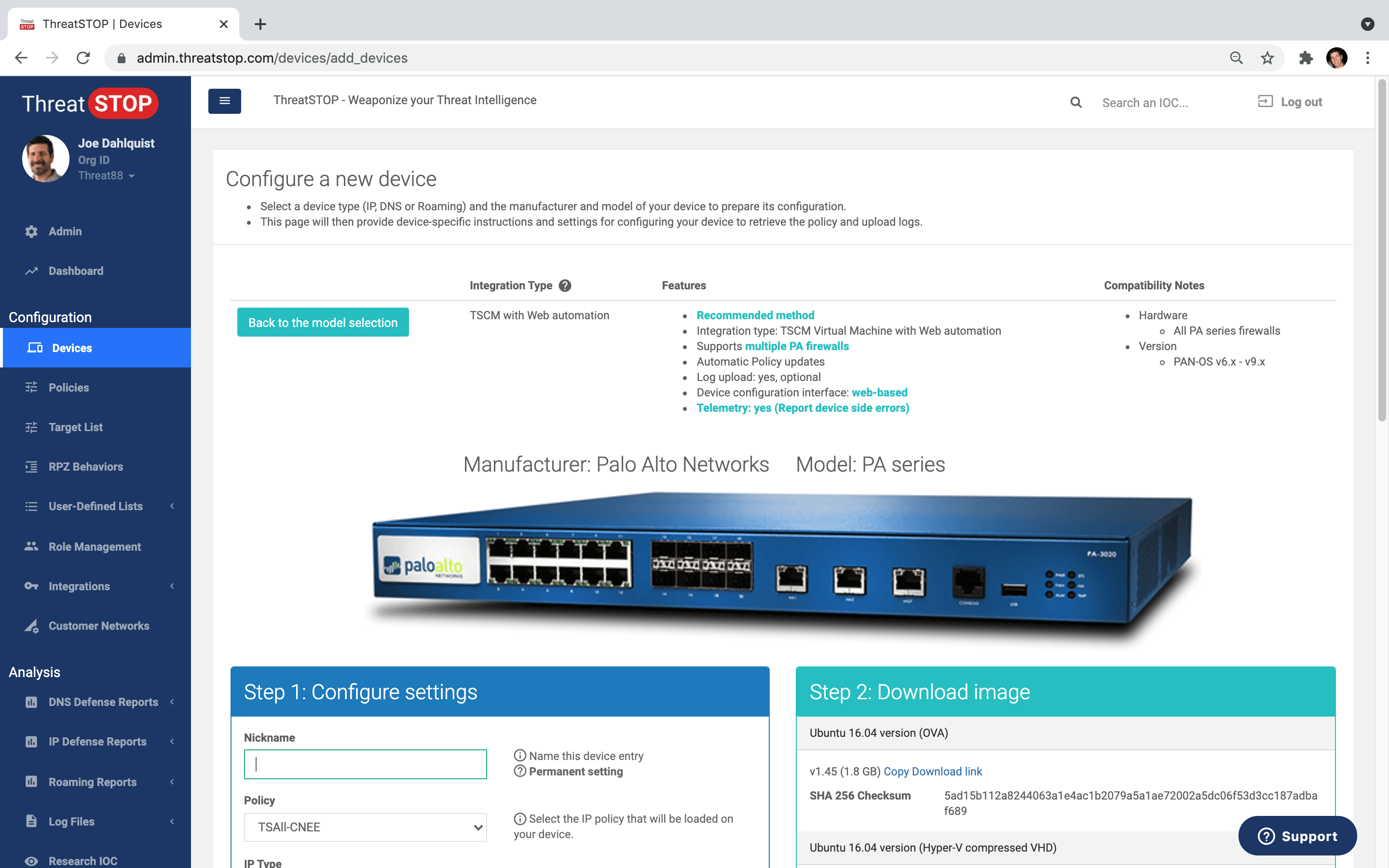
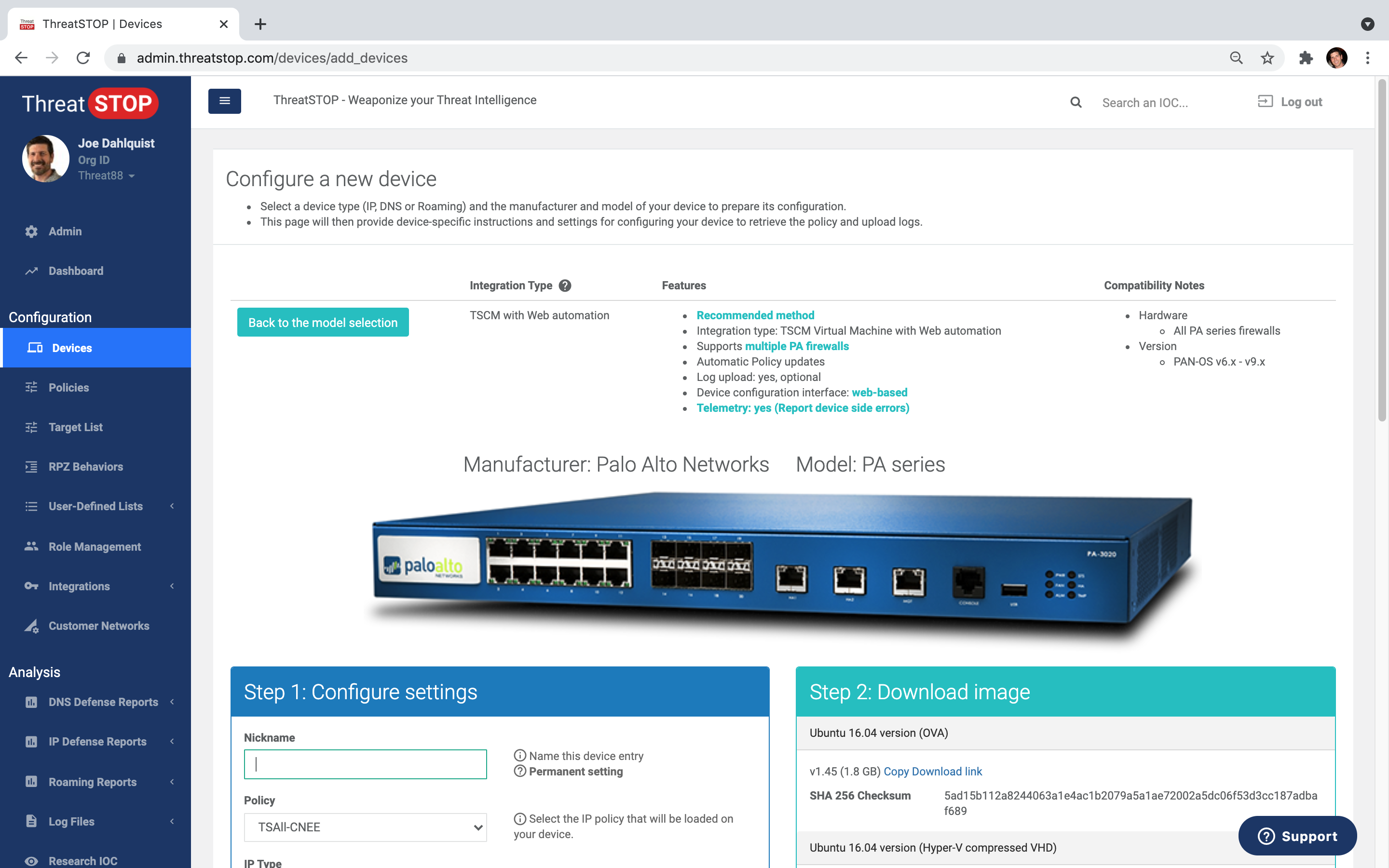
Device integration
Automated policy updates NGFW, DNS, Router, Switch, IDP, WAF, SIEM and more.
Advanced reporting
View & analyze blocked threats. Identify affected client devices. Custom email reports & alerts.
Save Time
- Automate and outsource essential 24/7 security policy updates.
- Rich reports in our portal or your SIEM.
- Rapidly identify infected hosts.
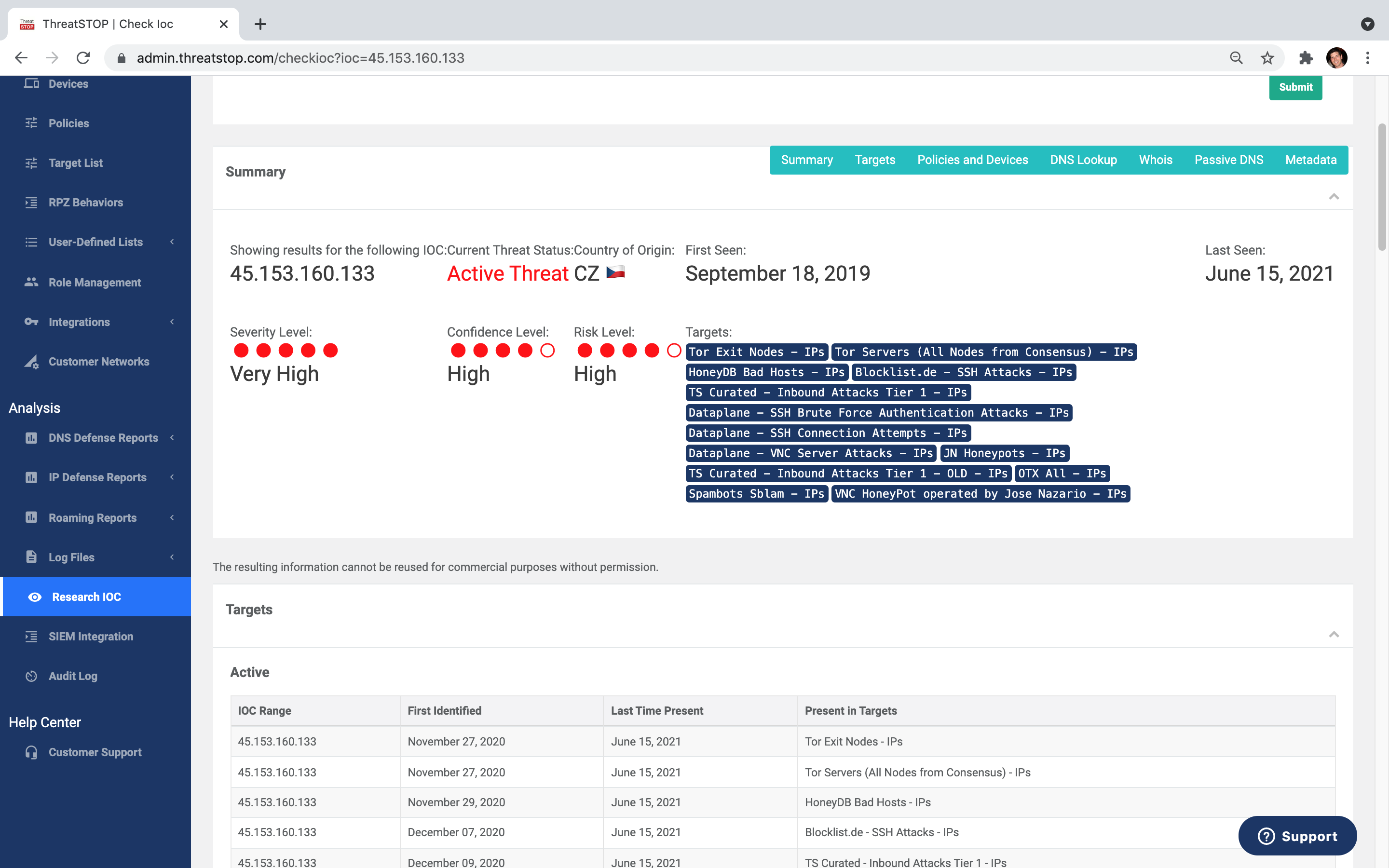
- Research tools, like Check IOC, included.
- Customize and schedule email reports and alerts.
Save Money
- Add powerful security to existing devices.
- Reduce endpoint infections and stop breaches.
- Reduce load on existing security layers.
- Eliminate unwanted bandwidth usage.
- Increase security and network efficiency.
Be More Secure
- Block connection attempts to criminal infrastructure on all ports and protocols.
- Continuous, automatic policy updates.
- Unique and valuable telemetry for SOC's and MSP's.
- Customize policies to match security postures.
- Multivendor security is always a feature, not a bug
How to deploy
Getting started is as simple as 5 easy steps.
Sign up for the service
Pick a security policy to use
Integrate DNS Defense with your device
Start automatically blocking threats
See reports detailing the protection
ThreatSTOP Platform
The ThreatSTOP platform is a SaaS security platform with modular product offerings for Protective DNS (PDNS), firewall automation, and other Threat Intel use cases. It integrates with physical, virtual, and hosted security stack components including firewalls, DNS servers, IDPS, SIEM and more. The platform automates threat intelligence acquisition, curation, and timely application for threat mitigation and visibility. Modules include:
DNS Defense
Using continuous updates from hundreds of Threat Intelligence sources, DNS Defense stops dangerous and unwanted DNS traffic before damage is done.
IP Defense
IP Defense sends automated policy updates to existing firewalls, routers and switches, and stops inbound attacks at network edges, before damage is done.
MyDNS
This takes the network DNS Defense Service and delivers it to individual endpoints, providing the same security even when these endpoints are outside the corporate network.
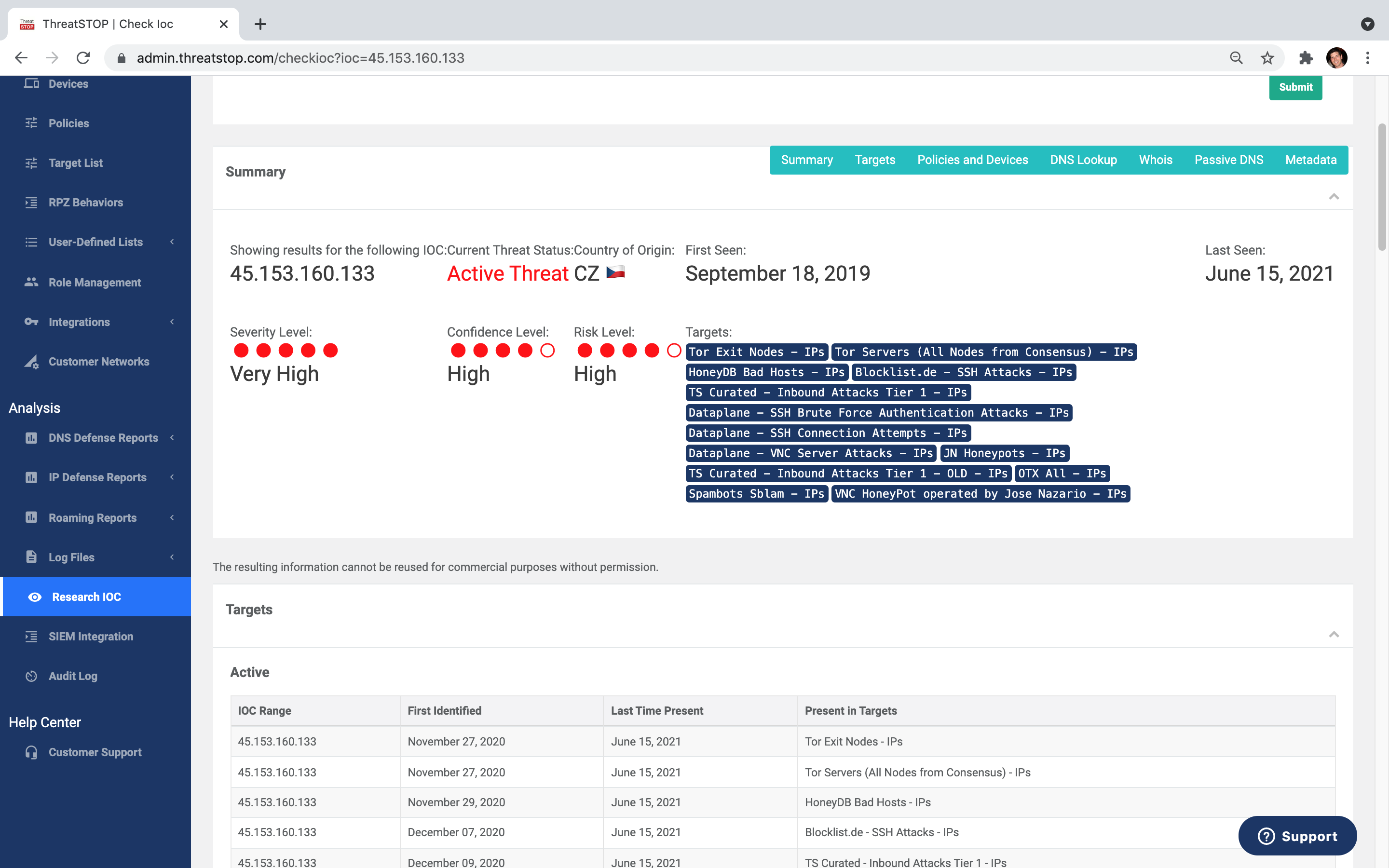
Check IoC Subscription
Check IOC is now available as a standalone subscription. We've made it easy to get your hands on tools that give you invaluable data, backed by one of the largest databases that we've been building for over a decade.
ThreatSTOP CE
The ThreatSTOP Community Account is our way of saying thank you to the security community for everything they do. A Community Account entitles you to run ThreatSTOP on one IP device (firewall, router, etc.) and one DNS device. Community accounts are limited to pre-built policies that include core protections such as the DShield Blocklist and Emergency Handler Blocks.
- DNS Defense CE
- IP Defense CE
- MyDNS CE
- Check IoC Tool
Threats blocked today
Updated every 15 minutes
Free Trial
See what your other security products have been missing. Start Stopping Threats today at the DNS layer. Quick, easy setup.
